Vous n'êtes pas connecté
- English
- Français
- عربي
- Español
- Deutsch
- Português
- русский язык
- Català
- Italiano
- Nederlands, Vlaams
- Norsk
- فارسی
- বাংলা
- اردو
- Azərbaycan dili
- Bahasa Indonesia
- Հայերեն
- Ελληνικά
- Bosanski jezik
- українська мова
- Íslenska
- Türkmen, Түркмен
- Türkçe
- Shqip
- Eesti keel
- magyar
- Қазақ тілі
- Kalaallisut ; kalaallit oqaasii
- Lietuvių kalba
- Latviešu valoda
- македонски јазик
- Монгол
- Bahasa Melayu ; بهاس ملايو
- ဗမာစာ
- Slovenščina
- тоҷикӣ ; toğikī ; تاجیکی
- ไทย
- O'zbek ; Ўзбек ; أۇزبېك
- Tiếng Việt
- ភាសាខ្មែរ
- རྫོང་ཁ
- Soomaaliga ; af Soomaali
Rubriques :
 Maroc - ITSECURITYNEWS.INFO - A La Une - 27/Sep 02:32
Maroc - ITSECURITYNEWS.INFO - A La Une - 27/Sep 02:32
Cybersecurity Compass: Bridging the Communication Gap
Discover how to use the Cybersecurity Compass to foster effective conversations about cybersecurity strategy between non-technical and technical audiences, focusing on the phases of before, during, and after a breach. This article has been indexed from Trend Micro Research, News…
Articles similaires
How Ransomhub Ransomware Uses EDRKillShifter to Disable EDR and Antivirus Protections
Trend Micro tracked this group as Water Bakunawa, behind the RansomHub ransomware, employs various anti-EDR techniques to play a high-stakes game of...
Việt Nam hopes for further cooperation with OECD at UN forums: Ambassador
The ambassador highlighted that the organisation could have a significant part in bridging the substantial gap between developed and developing...
On Influence Operations: Brainpower As A Weapon Of Choice – Analysis
By G.L. Lamborn Of Sweet Potatoes and Newsreels (FPRI) -- During the American Revolution, a British officer was sent from Charleston under flag...
The LLM Car: A Breakthrough in Human-AV Communication
As autonomous vehicles (AVs) edge closer to widespread adoption, a significant challenge remains: bridging the communication gap between human...
Earth Baxia Uses Spear-Phishing and GeoServer Exploit to Target APAC
We observed Earth Baxia carrying out targeted attacks against APAC countries that involved advanced techniques like spear-phishing and customized...
Cybersecurity Skills Gap Leaves Cloud Environments Vulnerable
A new report by Check Point Software highlights a significant increase in cloud security incidents, largely due to a lack of cybersecurity expertise...
Doing Business In The MENA Region – Analysis
What is the MENA region? MENA is the acronym for “Middle East and North Africa”, regularly used in academic and business writings. It refers...
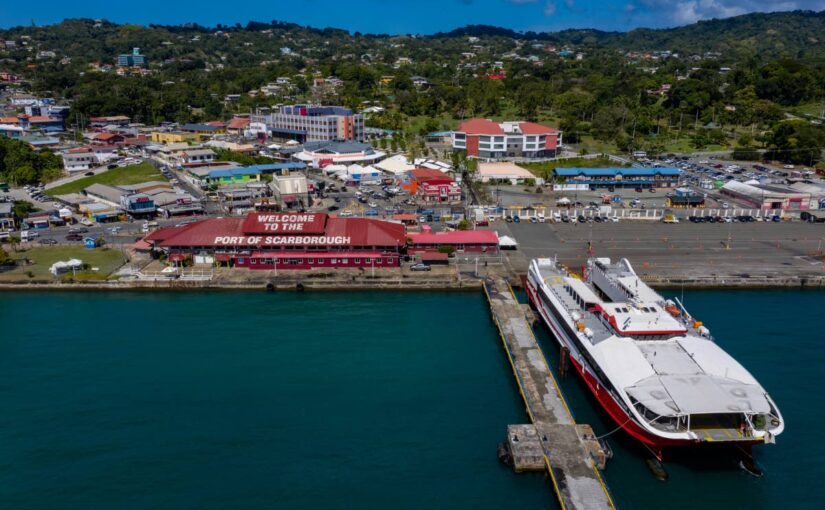
Amcham: Trinidad and Tobago’s economic development hinges on digital acceleration
WITH the International Monetary Fund (IMF) projecting moderate growth of 2.4 per cent for TT, the American Chamber of Commerce of TT (AmchamTT) has...
Les derniers communiqués
-
Villeroy & Boch joins the ranks of Europe's largest manufacturers of bathroom products
Villeroy & Boch - 01/03/2024