One of the things that became a hot conversation for a day or two was related to the implementation of DNS redirection by internet service providers...
Vous n'êtes pas connecté
- English
- Français
- عربي
- Español
- Deutsch
- Português
- русский язык
- Català
- Italiano
- Nederlands, Vlaams
- Norsk
- فارسی
- বাংলা
- اردو
- Azərbaycan dili
- Bahasa Indonesia
- Հայերեն
- Ελληνικά
- Bosanski jezik
- українська мова
- Íslenska
- Türkmen, Түркмен
- Türkçe
- Shqip
- Eesti keel
- magyar
- Қазақ тілі
- Kalaallisut ; kalaallit oqaasii
- Lietuvių kalba
- Latviešu valoda
- македонски јазик
- Монгол
- Bahasa Melayu ; بهاس ملايو
- ဗမာစာ
- Slovenščina
- тоҷикӣ ; toğikī ; تاجیکی
- ไทย
- O'zbek ; Ўзбек ; أۇزبېك
- Tiếng Việt
- ភាសាខ្មែរ
- རྫོང་ཁ
- Soomaaliga ; af Soomaali
 Maroc - VIETNAMNEWS.VN - Economy - 30/Aug 01:54
Maroc - VIETNAMNEWS.VN - Economy - 30/Aug 01:54
Better cybersecurity needed to protect data
Personal data has been leaked and posted publicly, and it has become a source of information for automated collection programmes used by fake websites or cybercrime organisations.
Articles similaires
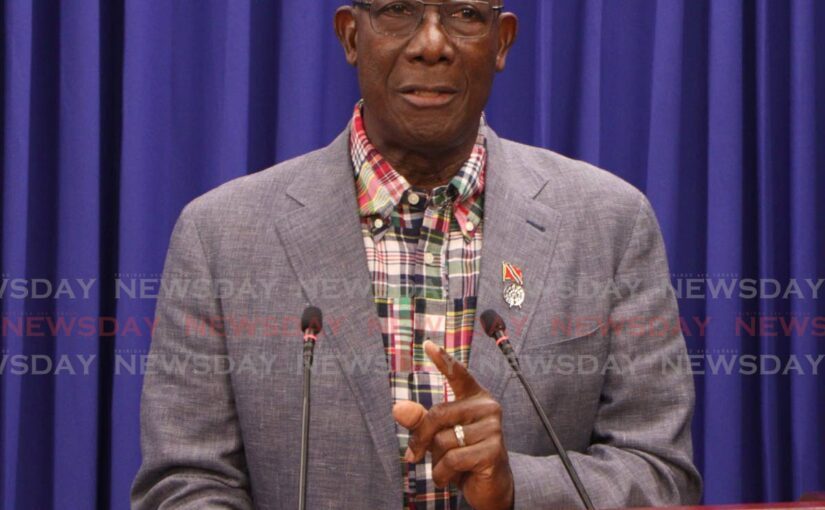
Government failing to protect citizens
THE EDITOR: It is time for the Government to take resolute action and demonstrate a genuine commitment to protecting its citizens. There have been...
Government failing to protect citizens
THE EDITOR: It is time for the Government to take resolute action and demonstrate a genuine commitment to protecting its citizens. There have been...
2 women die in Georgia after they couldn't access legal abortions and timely care
by Kavitha SuranaProPublica is a Pulitzer Prize-winning investigative newsroom. Sign up for The Big Story newsletter to receive stories like this one...
Researchers Details Attacks On Air-Gaps Computers To Steal Data
The air-gap data protection method isolates local networks from the internet to mitigate cyber threats and protect sensitive data, which is commonly...
Researchers Details Attacks On Air-Gaps Computers To Steal Data
The air-gap data protection method isolates local networks from the internet to mitigate cyber threats and protect sensitive data, which is commonly...
Disney Data Breach Exposes Sensitive Corporate and Personal Information
In July, Disney experienced a significant data breach that exposed far more than initially reported, compromising a wide array of sensitive...
Disney Data Breach Exposes Sensitive Corporate and Personal Information
In July, Disney experienced a significant data breach that exposed far more than initially reported, compromising a wide array of sensitive...
Cybersecurity Compliance and Beyond: How Protocols Drive Innovation and Growth
In today’s digital age, cybersecurity compliance is no longer just a legal necessity or a defensive measure; it has become a catalyst for innovation...
Cybersecurity Compliance and Beyond: How Protocols Drive Innovation and Growth
In today’s digital age, cybersecurity compliance is no longer just a legal necessity or a defensive measure; it has become a catalyst for innovation...
Les derniers communiqués
-
Aucun élément